Trends in Validation of DDoS Research - ScienceDirect.
Excerpt from Research Paper: Auditing, Monitoring, and Detecting of Dos or DDoS Attacks A Dos (denial of service attack) is an attempt to make network or machine resources non-available to legitimate users.
Radware ERT Research Paper. While Performing DDoS Attacks Can You Stay Anonymous While Participating in a DDoS Attack? Key Findings Taking part in a Hacktivist group is completely different than being part of a Botnet. In the Botnet, case participants are recruited to an attack without their knowledge, and in the Hacktivist group, case members knowingly take part in attack activities.
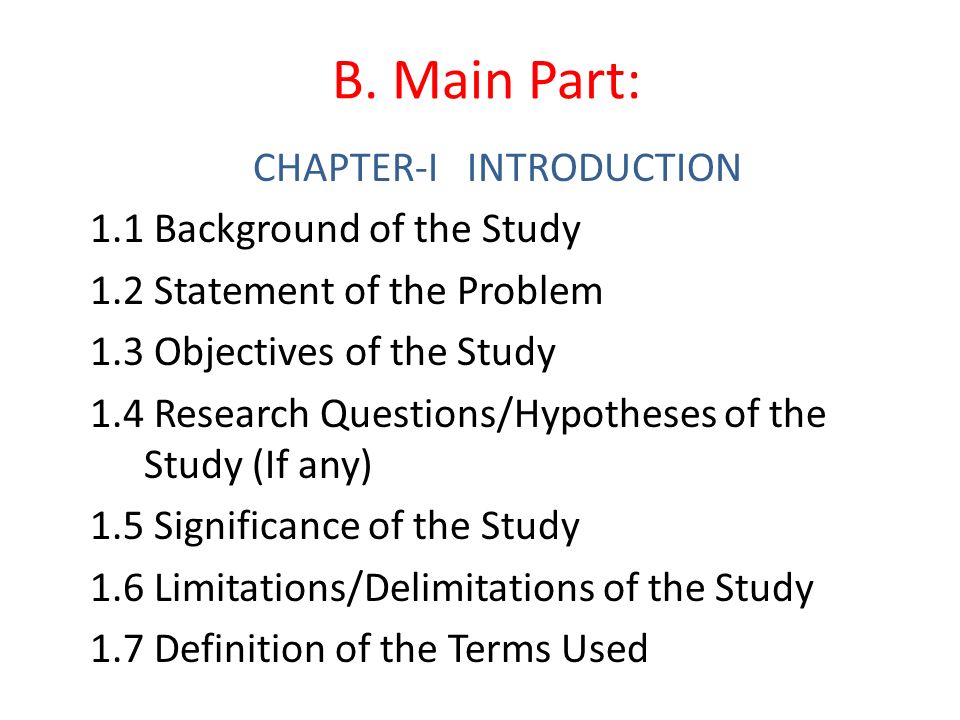
This paper first details the available datasets that scholars use for DDoS attack detection. The paper further depicts the a few tools that exist freely and commercially for use in the simulation programs of DDoS attacks. In addition, a traffic generator for normal and different types of DDoS attack has been developed. The aim of the paper is.
Occasionally, we can pinpoint the exact reason for an attack. A while back we noticed a DDoS attack against a university, so we activated the foundation DDoS mitigation service, which reduces the impact of an attack. A couple of hours later the same institution was targeted again.
Excerpt from Research Paper: Detecting, Preventing or Mitigating Distributed Dos (DDOS) Attacks The Internet continues to be a critical subject due to the increasing attacks based on the major universal communication infrastructures.
Finally in this research paper can be used by researchers to answer many important questions related to DDoS attack and their Novel solutions. II. D OS AND DDOS ATTACK OVERVIEW Denial of service attack is a form of cybercrime in which attackers overload computing or network resources with so much traffic that legitimate users are unable to gain access to those resources. Attacks are called.
Nowadays, DDoS attack has become more complex and modern for most IDS to detect. Adjustable and configurable traffic generator is becoming more and more important. This paper first details the available datasets that scholars use for DDoS attack detection. The paper further depicts the a few tools that exist freely and commercially for use in the simulation programs of DDoS attacks. In.